Embedded Consumer Wallets
Embed wallets directly into your consumer application
Spin up non-custodial wallets with built-in authentication, recovery, and transaction execution.


























Launch fast, control the full UX

Non-custodial wallets
Launch consumer wallets with hardware-isolated keys, using pre-built components and SDKs – live in under 7 minutes.

Flexible authentication and recovery
Configure passkey, email, or social login authentication for secure and user-friendly onboarding and recovery flows.

Transaction execution and gas sponsorship
Sponsor gas and execute onchain transactions end-to-end, from construction to broadcast.
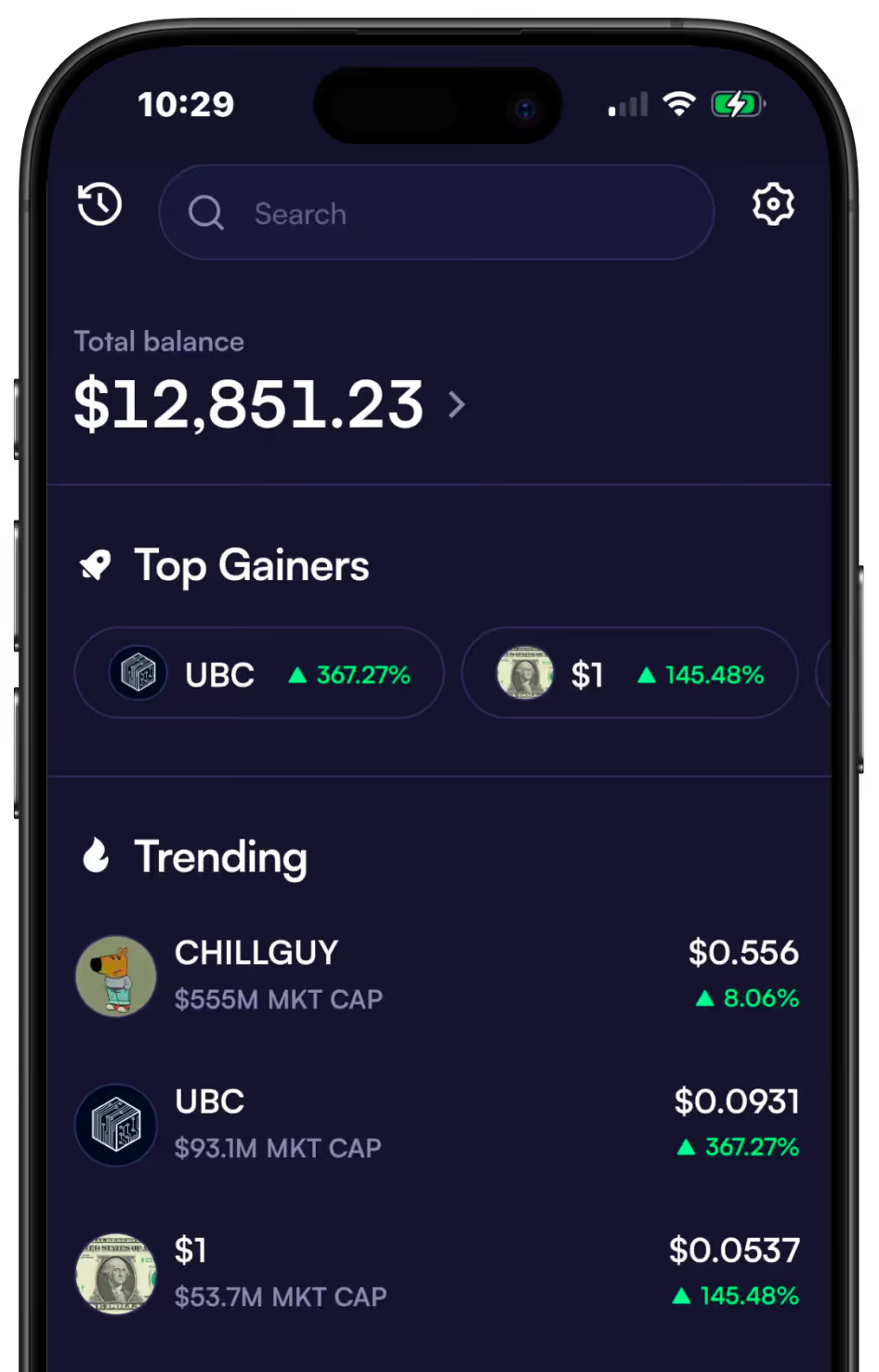
Moonshot uses Turnkey for a flawless mobile onboarding experience
Challenge
Moonshot’s vision was to make onchain trading as easy as buying stocks, so that anyone can buy and sell crypto in just a few clicks.
Solution
Moonshot built a seamless and secure onboarding process that simplifies wallet creation and signing, with Turnkey’s Embedded Consumer Wallets.
Learn more
Results
1.5M+ user wallets created
99.99% uptime since launch
2 weeks to full integration





How this works
Get started with Embedded Consumer Wallets in a few simple steps.
Set up an org in the Turnkey dashboard and determine how users will authenticate (e.g., email OTP, passkeys, OAuth).
Integrate the Turnkey SDK to manage authentication and wallet operations, ensuring users have secure, immediate access upon login.
Surface basic wallet functionality, like signing transactions or viewing addresses, directly within your app's UX.
Infrastructure that scales with your growth
Primitives flexible enough to evolve with your product. Infrastructure proven to run at scale.


Instant in-app transactions
Deliver instant, high-frequency crypto interactions at sub-100ms signing that feel native to your users.

User-friendly experiences across chains
Onboard users faster with familiar authentication methods like passkey, email or social logins.

Secure your users’ keys
Keep keys encrypted and never exposed, with signing and policies running inside secure enclaves so users retain full control.

Composable from day one
Start with UI plugins and drop down to low-level primitives like authentication methods, sessions, and recovery as you evolve.



