
Encryption Key Storage
Encrypt sensitive data with policy-gated key storage
Store encryption keys in secure enclaves, isolated from the data they protect.






























Launch user-friendly, encrypted recovery flows
Isolated key storage
Store encryption keys in secure enclaves and keep encrypted credentials on your platform, eliminating any single point of compromise.
Flexible authentication
Gate decryption through seamless user authentication like passkeys, OAuth, or OTP to match your existing flows and security requirements.

Authorization policies
Require quorum approvals and restrict access to specific users or systems for highly sensitive key exports.
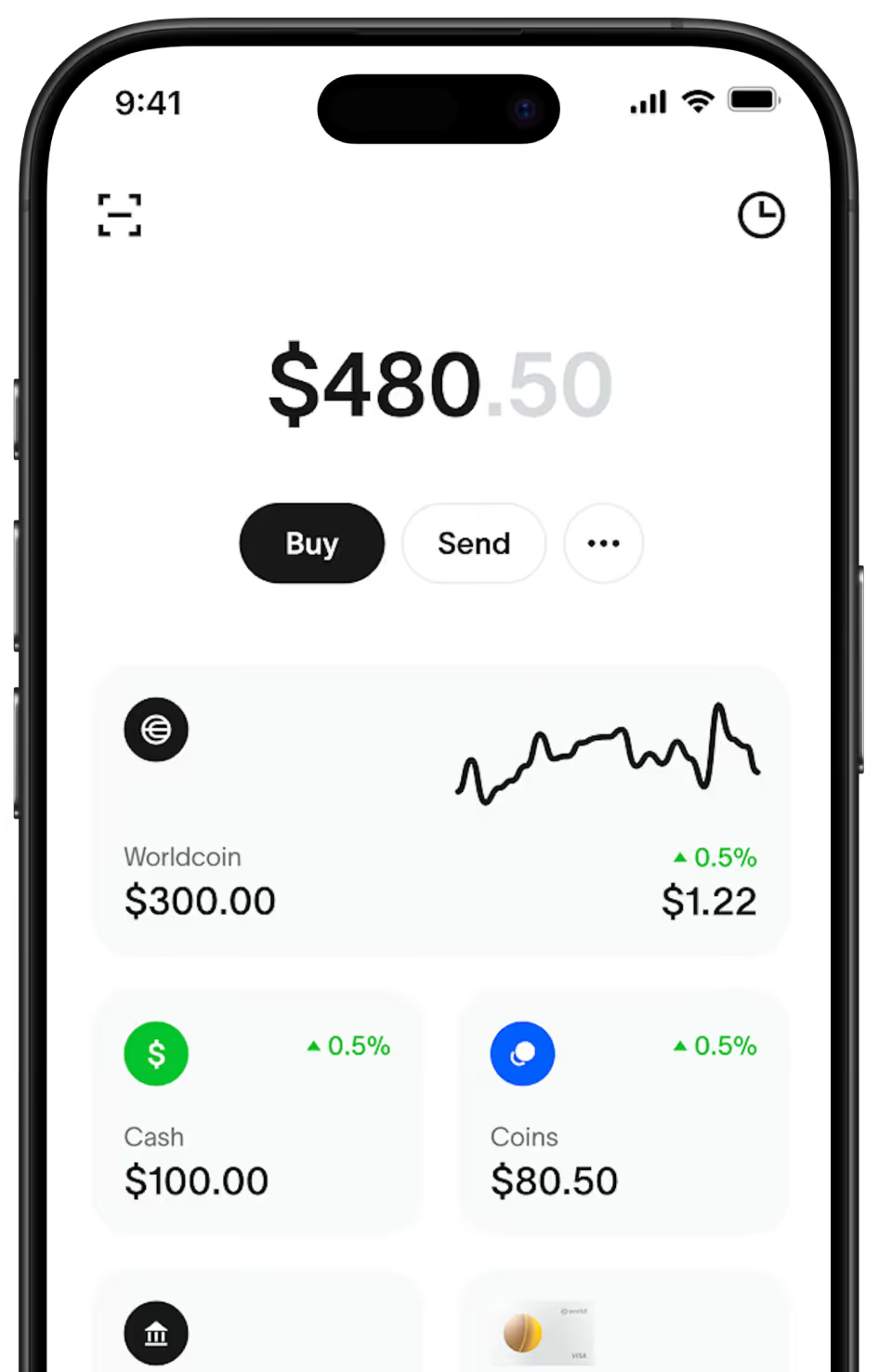
World App secures account recovery with user-gated encryption key management
Challenge
World App users rely on a "recovery bundle" to protect access to their World ID and assets, but could get stuck if they lost access to both their account and bundle.
Solution
World App built a programmable recovery system where the bundle's encryption key is stored in Turnkey’s secure enclaves, only accessible through a user’s OAuth. Learn more
Results
Enhanced user recoverability without compromising on privacy
Users remain in control through flexible recovery
Expanded access to digital proof with user trust and safety



How this works
Get started with Encryption Key Storage in a few simple steps.
Isolate the encryption key in Turnkey’s secure enclave, ensuring it is never exposed.
Use built-in authentication and policies to manage key access.
Decrypt recovery bundles locally, then clear the decryption key and data from memory.
Encryption key security at every stage
Designed to protect encryption keys throughout their lifecycle, so no single party can access them alone, not even Turnkey.


Secure key transport
Export encryption keys from secure enclaves using Hybrid Public Key Encryption (HPKE), without exposing keys in transit.

Lightning-fast decryption
Retrieve encryption keys once and decrypt locally in milliseconds, for fast and seamless user-controlled recovery flows.

Verifiable key control
Independently prove that no one, even Turnkey, can export encryption keys without meeting your access requirements.

Full audit trails
Track every key export event from secure enclaves, capturing who accessed the keys and who authorized the request.



